Overview
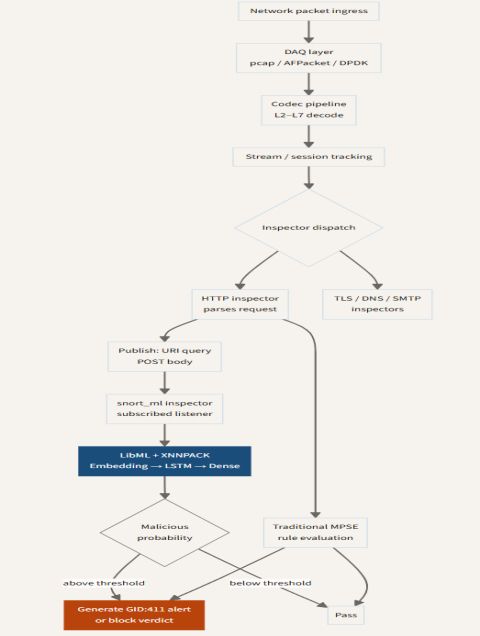
The traditional intrusion detection system (IDS) has long relied on signature-based methods: a database of known attack patterns is compared against network traffic. When a match occurs, an alert is raised. This approach is effective against known threats but fails against zero-day attacks, polymorphic malware, and sophisticated adversaries who can modify their behavior. The emergence of machine learning (ML) and agentic AI—autonomous agents that perceive their environment, reason, and act—has fundamentally changed the question. Instead of asking "Does this match a known pattern?" modern detection asks "Does this behavior make sense in context?" This tutorial explores how to build a next-generation IDS that combines the speed of signature matching with the adaptability of ML-driven agents, using the conceptual framework of SnortML. It provides a step-by-step guide to integrating a machine learning module with Snort, enabling your system to not only detect known threats but also flag anomalous, contextually suspicious activities.
Prerequisites
Knowledge Requirements
- Basic understanding of network protocols (TCP/IP, HTTP, DNS)
- Familiarity with intrusion detection concepts and tools (preferably Snort)
- Intermediate programming skills in Python (for ML integration)
- Basic machine learning concepts (features, classification, anomaly detection)
Technical Requirements
- A Linux-based system (Ubuntu 20.04+ recommended) with root access
- Snort 3.0 installed and configured (official site)
- Python 3.8+ with libraries: pandas, scikit-learn, joblib, and pyshark
- A sample PCAP file for testing (malware-traffic-analysis.net)
- Basic understanding of agentic AI: autonomous decision-making loops (perception-action)
Step-by-Step Instructions
1. Extending Snort with a Machine Learning Module
Snort's architecture allows custom preprocessors and output plugins. We'll create a Python-based agent that communicates with Snort via a Unix socket to receive alerts and respond with contextual decisions.
- Enable JSON output in Snort: Modify
snort.luato add an output plugin that sends alerts to a Unix socket.
-- In snort.lua
json_output = {
alert_to = "/tmp/snort_alert.sock",
format = "json"
}- Create a Python socket listener: This script will read alerts, extract features (e.g., packet length, flags, timestamps), and pass them to an ML model for classification.
import socket, json, sys
sock = socket.socket(socket.AF_UNIX, socket.SOCK_STREAM)
sock.bind("/tmp/snort_alert.sock")
sock.listen(1)
conn, addr = sock.accept()
while True:
data = conn.recv(1024)
if not data: break
alert = json.loads(data.decode())
# Extract features and run ML decision
# Placeholder: call classify(alert)2. Building the Machine Learning Model
We'll train a model on labeled network traffic (benign vs. malicious). Use Random Forest for its interpretability and robustness.
- Step 1: Feature Engineering – Extract from packets: packet length, TTL, window size, protocol, and inter-arrival time. Use Scapy or pyshark to process PCAP.
- Step 2: Training – Split data, train, and save the model.
from sklearn.ensemble import RandomForestClassifier
from sklearn.model_selection import train_test_split
import pandas as pd
df = pd.read_csv("network_features.csv")
X = df.drop("label", axis=1)
y = df["label"]
X_train, X_test, y_train, y_test = train_test_split(X, y, test_size=0.2)
model = RandomForestClassifier(n_estimators=100)
model.fit(X_train, y_train)
# Save model for later use
import joblib
joblib.dump(model, "snortml_model.pkl")3. Creating an Agentic Loop
An agentic AI goes beyond static ML: it can request additional context (e.g., DNS lookups, previous alerts) and decide whether to escalate, block, or ignore. Implement a simple feedback loop inside the Python listener.
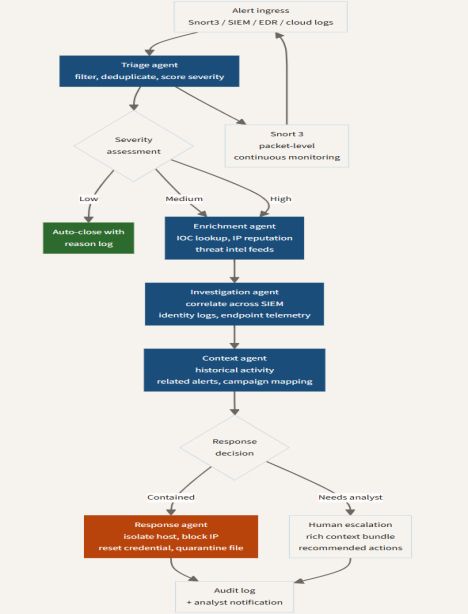
def decide_action(alert, model, context_store):
features = extract_features(alert)
prediction = model.predict([features])[0]
if prediction == 1: # potential threat
# check context: does this IP appear in other alerts?
ip = alert['src_ip']
if ip in context_store and context_store[ip] > 3:
return "block"
else:
return "flag_for_review"
else:
return "ignore"
# context_store is a dict tracking IP alert counts4. Integrating the Agent with Snort
Modify the Snort configuration to run the Python script as a preprocessor plugin or as an external service. For simplicity, run the Python listener in a separate process and start Snort with snort -c snort.lua -i eth0 --plugin-path /path/to/plugin.
5. Testing the System
Use a known malicious PCAP (e.g., from a CTF) and a benign PCAP. Monitor the /tmp/snort_alert.sock for decisions. Verify that the agent correctly flags anomalies and blocks high-confidence threats.
Common Mistakes
Overfitting the ML Model
Training on a limited dataset will cause the model to memorize rather than generalize. Always use diverse traffic captures and cross-validate.
Ignoring Feature Scaling
Tree-based models are scale-invariant, but if you later switch to SVM or neural networks, failing to standardize features will degrade performance.
Socket Timeouts in High-Throughput Networks
If the Python agent cannot process alerts fast enough, Snort will hang or drop alerts. Use asynchronous I/O (asyncio) or run the listener with a dedicated queue (e.g., Redis).
Treating Agent Decisions as Infallible
Agentic AI should augment, not replace, human analysis. Always include a logging mechanism that allows security analysts to review false positives and adjust the model.
Summary
This tutorial demonstrated how to evolve a signature-based IDS like Snort into a contextual, intelligent detection system using machine learning and agentic AI. By feeding Snort alerts into a Python-based agent that runs a trained random forest model, you can detect not only known attacks but also unusual behaviors that deviate from normal traffic patterns. The agent adds a decision-making layer—blocking, flagging, or ignoring based on context—transforming the IDS from a simple pattern matcher into a proactive security entity. Key takeaways: extend Snort with a Unix socket, train an ML model with well-chosen features, implement an autonomous agent loop, and avoid common pitfalls like overfitting and performance bottlenecks. The result is a system that asks not just "Does this match?" but "Does this make sense?"—a crucial step in modern cybersecurity.